Вызовы (challenges) в реализации DPI методом полного протокольного декодирования
Пономаренко Роман
http://t.me/rerand0m
rerandom@ispras.ru
Модель OSI
"Глубина" разбора
"Глубина" разбора

Применение DPI
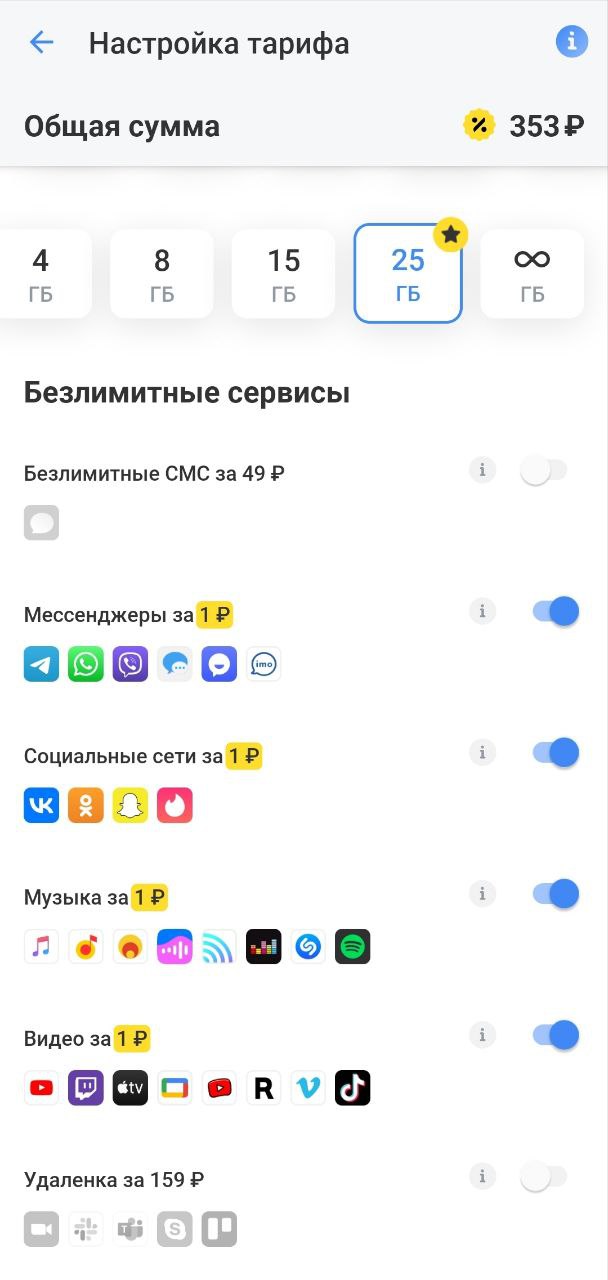
Классификация приложений и пользователей
- Тарификация
- Управление доступом
Применение DPI
Выделение полезной нагрузки 7 уровня модели OSI
- DLP
Применение DPI
Выявление особых признаков
- Выявление и анализ атак
- Балансировка нагрузки

Применение DPI
Отладка
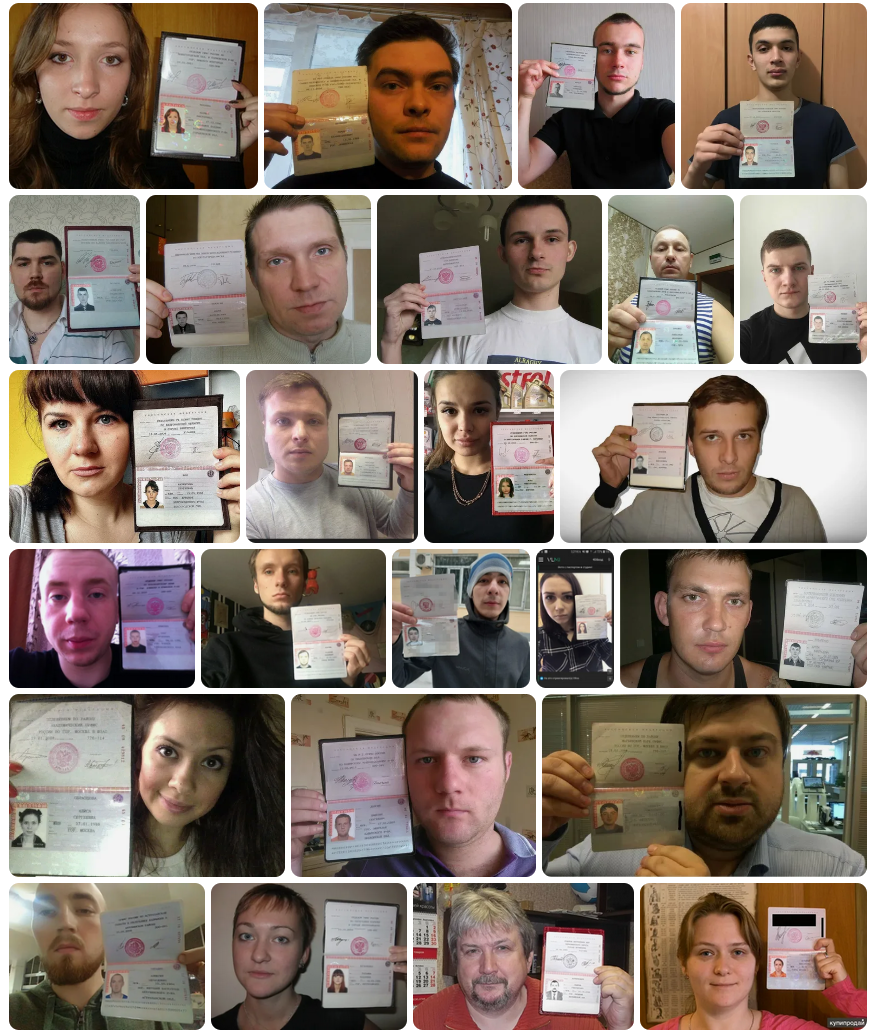
Сетевая криминалистика

Подходы к реализации
- Классификация по портам и/или первым байтам полезной нагрузки
- Поиск признаков по шаблонам
- Применение методов машинного обучения
- Декодирование
Полное протокольное декодирование
IPS на Wireshark
Dodiya B., Singh U. Malicious traffic analysis using Wireshark by collection of indicators of compromise //Int J Comput Appl. – 2022. – Т. 183. – С. 975-8887.
Jaya I. K. N. A., Dewi I. A. U., Mahendra G. S. Implementation of Wireshark Application in Data Security Analysis on LMS Website //Journal of Computer Networks, Architecture and High Performance Computing. – 2022. – Т. 4. – №. 1. – С. 79-86.
Afzal R., Murugesan R. K. Implementation of a Malicious Traffic Filter Using Snort and Wireshark as a Proof of Concept to Enhance Mobile Network Security //Journal of Telecommunications and Information Technology. – 2022. – №. 1.
Ahmad R. Z. N. et al. A NMAP AND WIRESHARK APPLICATION FOR DATA ANALYSIS AND NETWORK SECURITY //JComce-Journal of Computer Science. – 2023. – Т. 1. – №. 1.
Архитектура в первом приближении
1. Захват
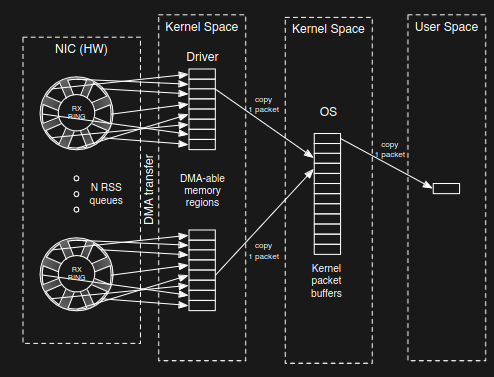
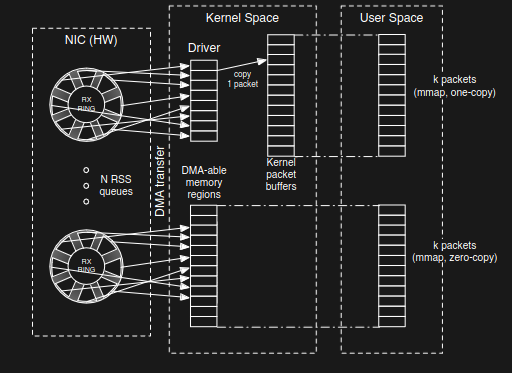
Как Linux захватывает пакеты?
1. Захват
Как Linux захватывает пакеты?
1. Захват
К чему стремимся
"Глубина" разбора
"Глубина" разбора Протосферой
2. Разбор
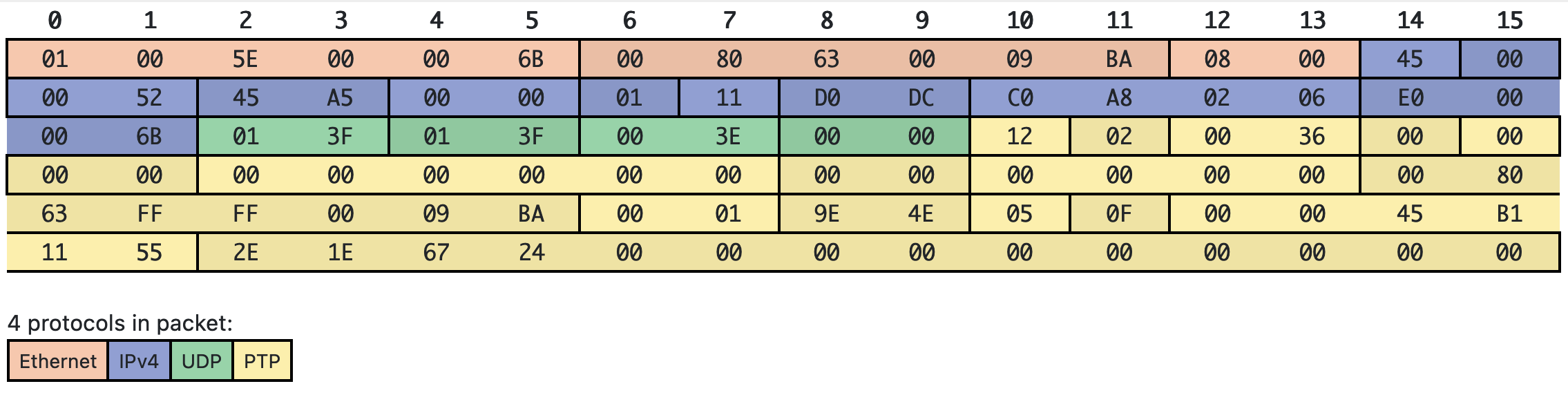
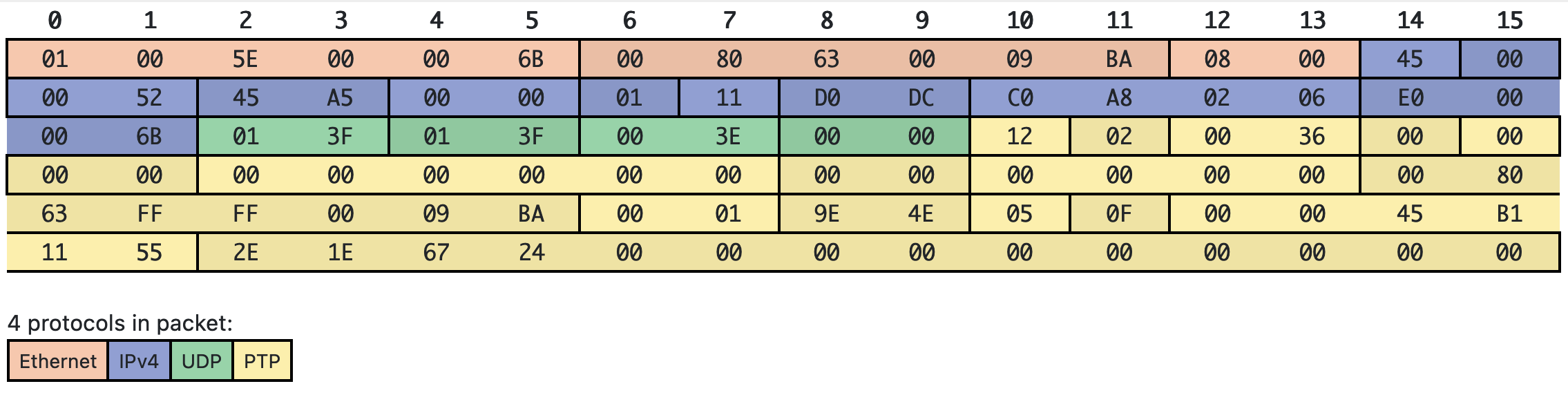
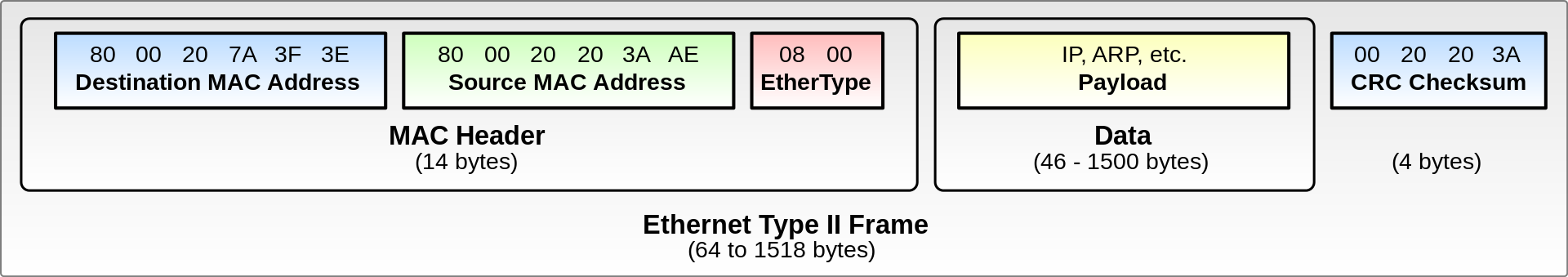
Инкапсуляция
Проблема на сеансовом уровне
3. Сборка сеансов

4. Сохранение состояния
5. Представление результатов

Архитектура в первом приближении
С модулями
Мы получили production-ready DPI! Да?

"Вторичные" проблемы
- Общее ускорение работы
- Управление памятью
- Расширение функционала
Общее ускорение работы
Распараллеливание
- Запуск в кластере
- Пул воркеров
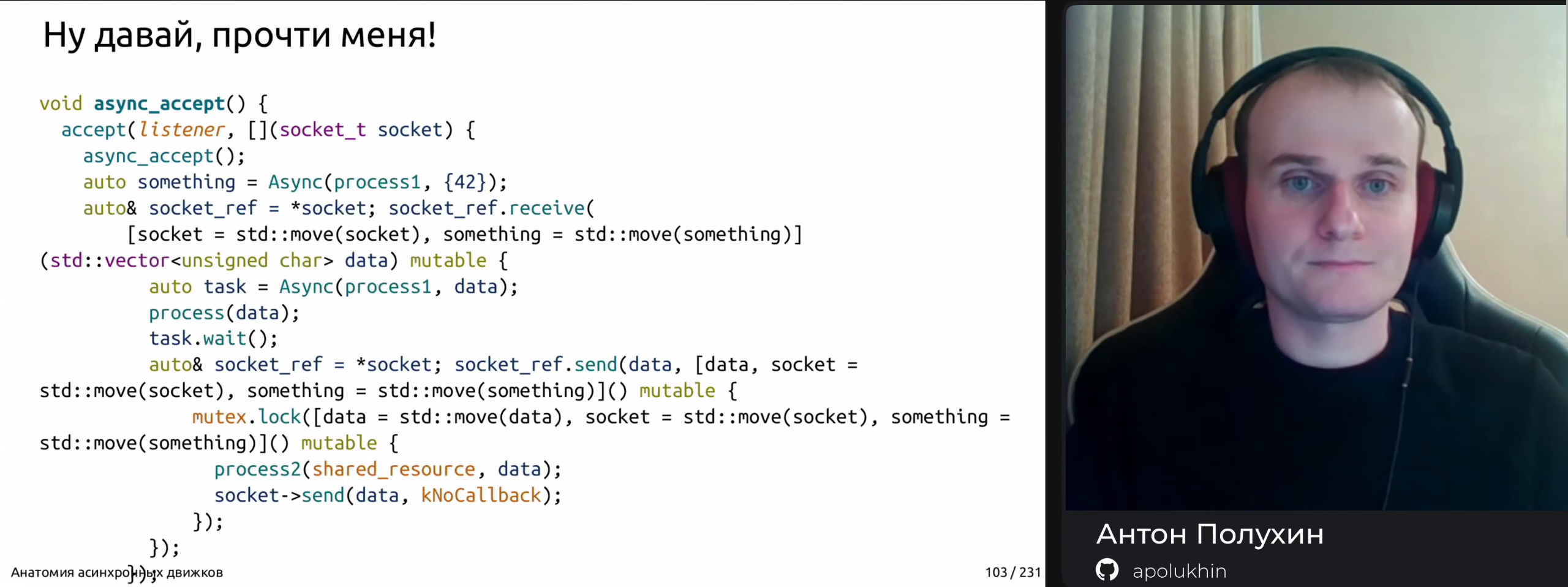
- Асинхронная обработка
Пул воркеров
Асинхронный код
Общее ускорение работы
- Отбрасывание всего "ненужного"
Управление памятью
static vs dynamic
 Я не нашёл подходящей картинки, наслаждайтесь этой.
Я не нашёл подходящей картинки, наслаждайтесь этой.
Управление памятью
Управление памятью
Большое количество копирований
Расширение функционала
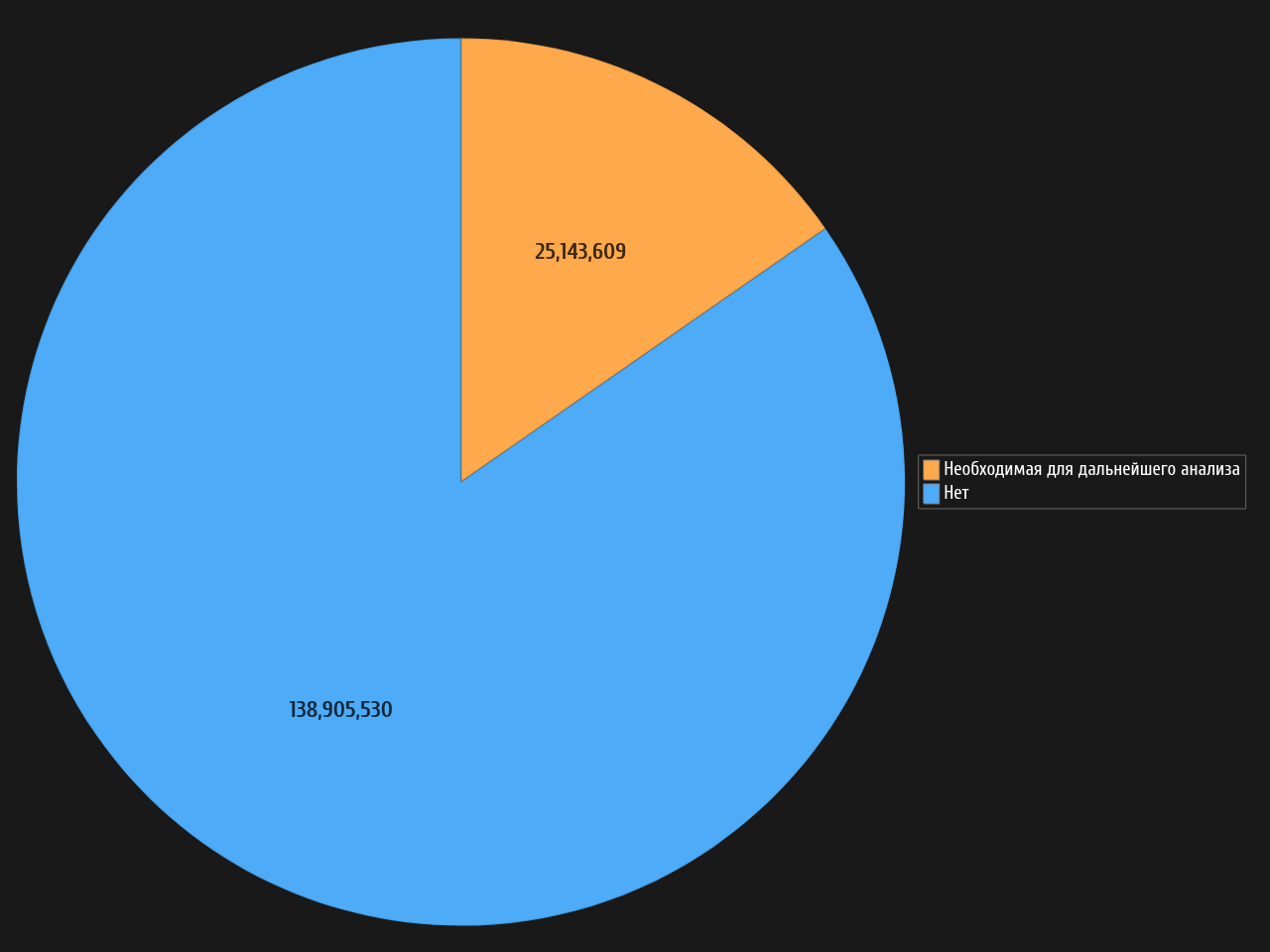
Эксперимент